What is Yguekcbe ransomware?
Yguekcbe ransomware is a malware program (a virus) that is designed to make money in a very specific way. First, it encrypts all files on the target computer using a cryptographic algorithm. This process renders the files inaccessible, but it is reversible. The virus then offers to do just that, to decrypt the files; that, however, would cost victim money. These viruses are called ransomware because this process essentially holds the files for ransom.
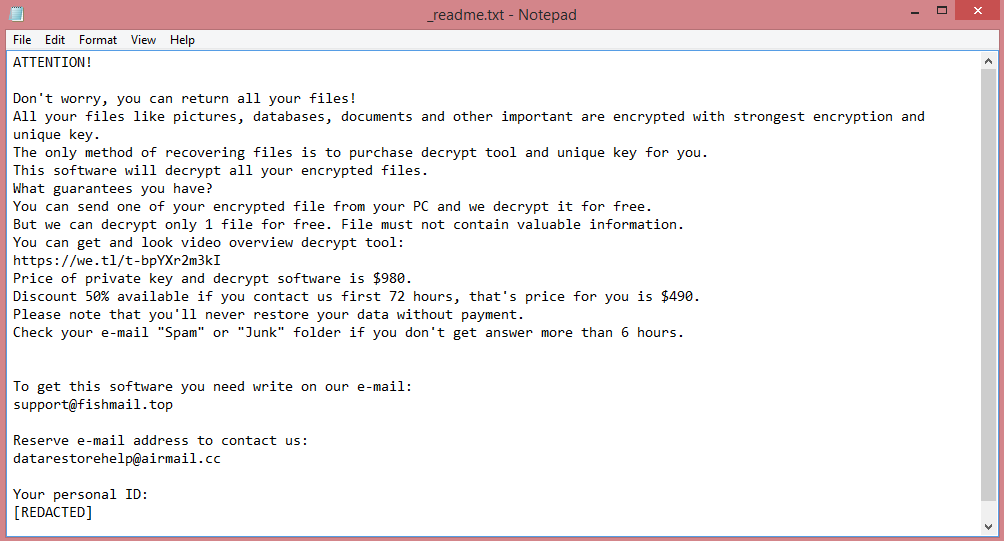
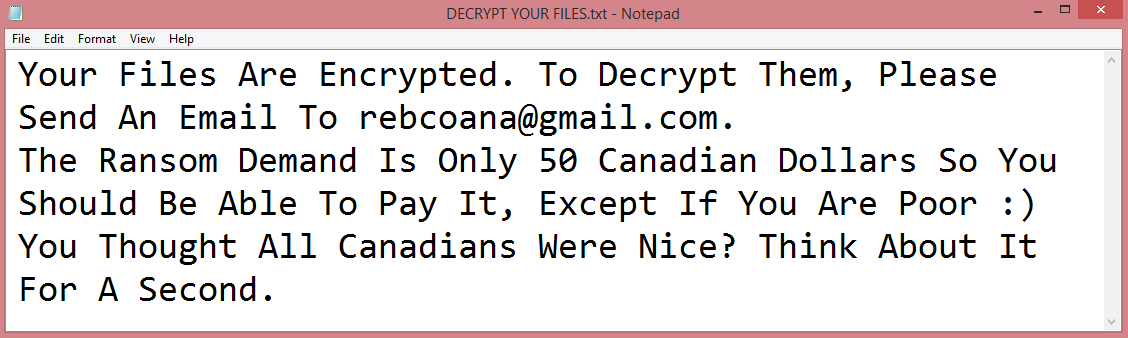
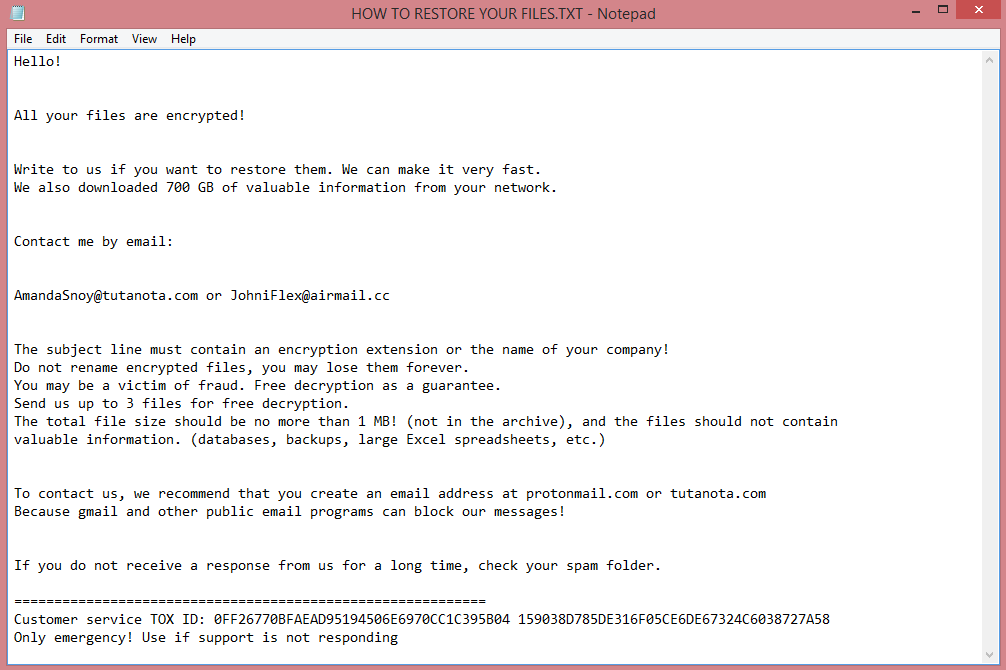
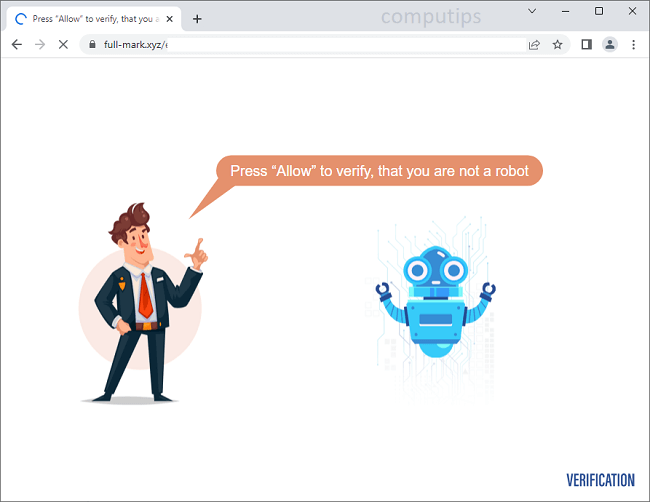
When Yguekcbe encrypts files, it also changes their names, adding .yguekcbe file extension. In fact, this is how the virus got its name. It also leaves a ransom note, “HOW TO RESTORE YOUR FILES.TXT”, on the Desktop. The image above contains the full text of the note, but we will also summarize it in the next paragraph.
The note indicates that Yguekcbe virus is designed to target companies, though of course, private individuals may also fall victim to it by accident. The hackers do not specify the ransom amount, only their contact information. Presumably this is because they intend to negotiate.
Contacting the hackers is a bad idea; in many cases they just ignore their victims after receiving payment. And if you really are just a citizen whose computer got infected with Yguekcbe by mistake, they likely wouldn’t even talk with you. This is why you should follow our guide, which will describe how to remove Yguekcbe ransomware and decrypt .yguekcbe files without their involvement.
![CryptBIT 2.0 ransom note:
Hello!
Now your files are crypted with the strongest millitary algorithms RSA4096 and AES-256.
In addition, all encrypted files have been sent to our server
and in the event of non-payment within 7 days,they will be made public.
Warning!
Do not rename encrypted files.
Do not try to decrypt your data using third party software.
You can only do damage to your files, lose your money and time.
In order to confirm that we are not scammers, you can send 2-3 files to the email address below.
Files should be less than 5 MB and contain no valuable data (Databases, backups, large excel sheets, etc.).
Please don't forget to write the name of your company in the subject of your e-mail.
You will receive decrypted samples.
To recover all files you must contact us for a private quote by the contact email.
You have to pay for decryption in Bitcoins.
P.S. Remember, we are not scammers.
We don't need your data or information but after 7 days all files and keys will be deleted automatically.
Write to us immediately after infection
All your files will be restored. We guarantee.
Contact email:
cryptbit2.0@protonmail.com
BTC wallet:
[REDACTED]
Have a nice day
CryptBIT 2.0 ransomware group
This is the end of the note. Below is a guide explaining how to remove CryptBIT 2.0 ransomware.](https://www.computips.org/wp-content/uploads/2022/11/how-to-remove-cryptbit-2.0-ransomware.png)