
How to remove My Recipe Finder browser hijacker


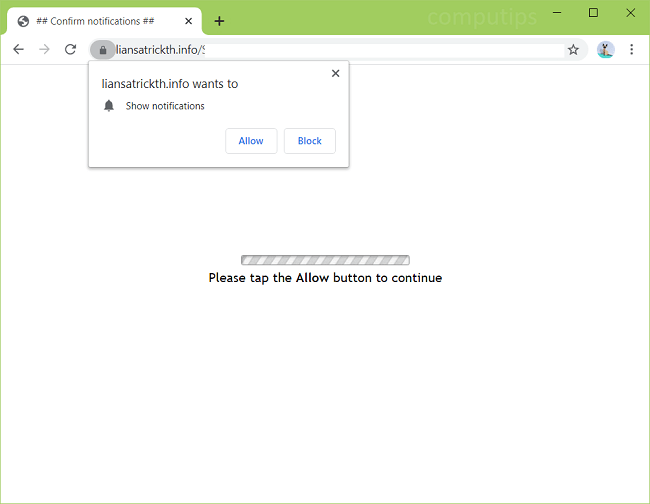
Liansatrickth.info is a deceptive website that attempts to trick users into accepting its notifications request. The site claims that users have to click or tap Allow on its notifications request box for one reason or another: to prove that they are not robots, to access a page, to remove ads from the site, etc. If someone clicks Allow, Liansatrickth.info notifications will begin to spam him or her, popping up time and again in the top-right or lower-right corner of the screen. Liansatrickth.info notifications will promote shady websites, prompt the user to follow clickbait links, download suspicious software, and so on. If Liansatrickth.info site keeps opening on your browser on its own, there may be adware installed on your Windows or Mac computer. This step-by-step guide will help you uninstall adware and remove Liansatrickth.info pop-ups and notifications from your browser.
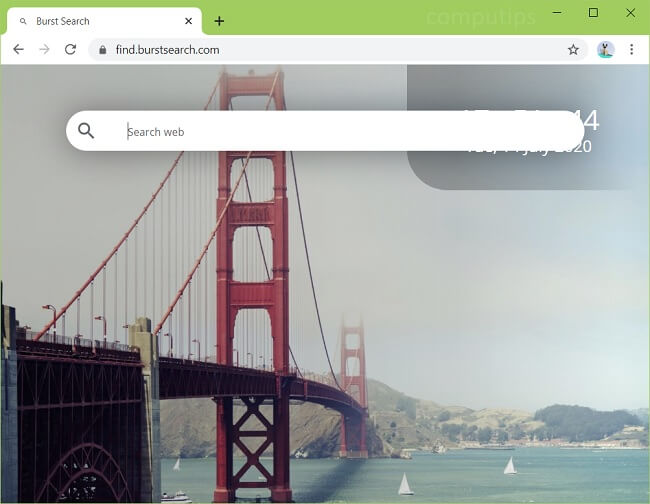
Burst Search (find.burstsearch.com) is a dubious search engine that your browser may start redirecting your searches to all of a sudden. If you investigate, you will find Burst Search browser extension on your Chrome browser that you will not be able to remove. Your browser will tell you that it is “Managed by your organization”, and you won’t be able to change default search engine because “Burst Search is controlling this setting”. Burst Search is a browser hijacker, that is, a piece of software capable of changing search engine and some other browser settings. The reason you cannot remove Burst Search from Chrome browser is that it adds a Chrome Group Policy to your computer settings so that Chrome “thinks” the extension is installed by an admin of your network. You may follow this step-by-step guide to uninstall Burst Search browser hijacker and remove find.burstsearch.com from your browser.
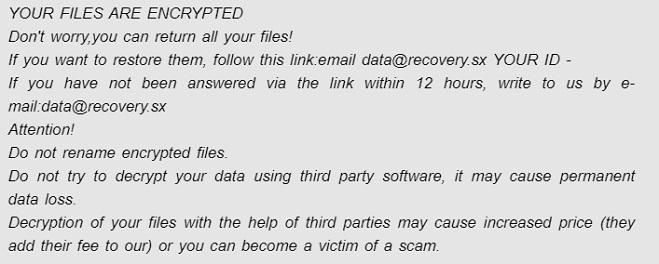
This is a malicious program that is part of the Dharma Ransomware family. According to experts this is one of the most powerful and popular families of viruses. It includes programs that infect systems with high speed by fraudulent methods. .data (Dharma) ransomware searches for important files for encryption and after that it requires payment for decryption. In the process of encryption all files are renamed the extension “.data” is added to the familiar name. After encryption is completed a file is created with the message “FILES ENCRYPTED.txt”

Files of the system that Smpl ransomware infected are encrypted with a malicious algorithm after which you cannot use or even open files. All infected files have the extension “.smpl“. This is a mark of infection of the file. Smpl ransomware can span absolutely any file, be it audio, photo, video or some kind of documentation. After infection Smpl ransomware creates “FILES ENCRYPTED.txt” text file with a note about infection

FunctionRecord is a virus of the advertising type that aims to infect Mac. After installation it runs a special infection algorithm. This is an advertising application, so the infection of the Mac occurs through the introduction of advertising and other notifications. FunctionRecord changes browser settings and promotes fake search engines to bring as many infections into the system as possible. In order to attract users and make them click on ads FunctionRecord monitors information related to your views and displays ads on a topic that is more interesting to you. Advertising, redirections greatly reduce the quality of viewing because they limit the speed of viewing and visibility of the site. Clicking on notifications not only infects the system and redirects victims to unnecessary sites but can also load some application without your consent. Your personal data that FunctionRecord captures will be transferred to third parties. Mac can be cleaned by removing FunctionRecord by automatic or manual methods.

Victims of virus infection claimed that before they learned about infection a huge amount of advertising appeared every day on the screen. This is one of the main signs of “Ads by Pop” adware infection. Virus is an adware application. Ad applications infect the system by using the introduction of advertisements that adversely affect the performance of the system. But advertising is not the only sign of infection. Due to changes in settings and the search engine your request in the search engine will be redirected to other pages. Virus displays ads in the form of pop-ups and ads. Usually, these are adult sites, online games, fake updates

This is a program that changes the home page and page of a new browser tab without knowledge of users. Your usual browser tab will be changed to MyDocsHere New Tab. Because of these changes you will be redirected to a new MyDocsHere tab every time you type in a search query. MyDocsHere will redirect you to unnecessary pages to benefit from clicks and views and your system will deteriorate. Users will not be able to undo these changes on their own until MyDocsHere has captured your truth.

REPL ransomware is a malicious program of one of the most powerful types of ransomware. It scans computer for files (video, pictures, audio, working documents: .doc, .docx, .xls, .pdf). When these files are discovered an extension “.repl” is added to their names to indicate that you can no longer open them. After encrypting all the data virus sent an email with information about the infection in the file “_readme.txt”

This is a ransomware species of Fonix. XINOF ransomware like all ransomware penetrates the system illegally to encrypt all files found on the computer. Virus adds the .XINOF extension to file names. If you see a file with this extension please understand that you can no longer use it and open it. After the encryption process a file is created in the form of a pop-up window. This message in the file informs about the infection invites victims who are looking for their important files to use the decryption key