
What Is Topi Ransomware?
Topi Ransomware is malware from the Djvu family. It finds important files on your computer and encrypts them with the “.topi” extension

Topi Ransomware is malware from the Djvu family. It finds important files on your computer and encrypts them with the “.topi” extension
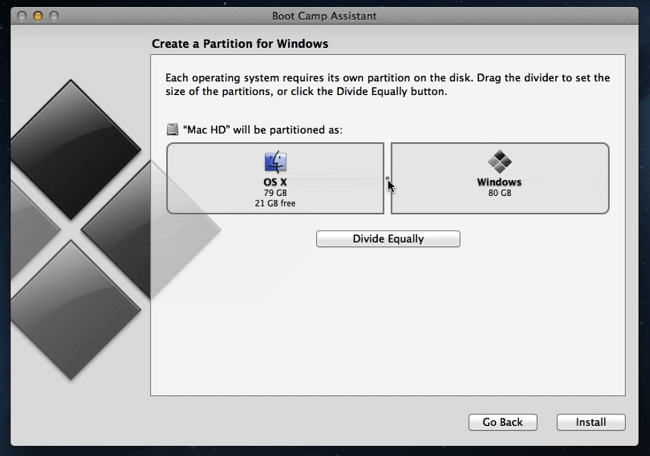
If you need to run Windows 8.1 on a Macbook, there are a few ways to do it: you can use Mac’s BootCamp Assistant or download and use a virtual machine like Parallels Desktop, VMware Fusion or VirtualBox. Unfortunately, installing Windows 8 via BootCamp will probably not work if your Macbook is newer than 2016. In that case virtualization software should still work if you have a Windows 8.1 license key. In this article we describe pros and cons of each method so that you can decide for yourself which one to use.

This is a viral deceptive app that changes your browser’s search engine
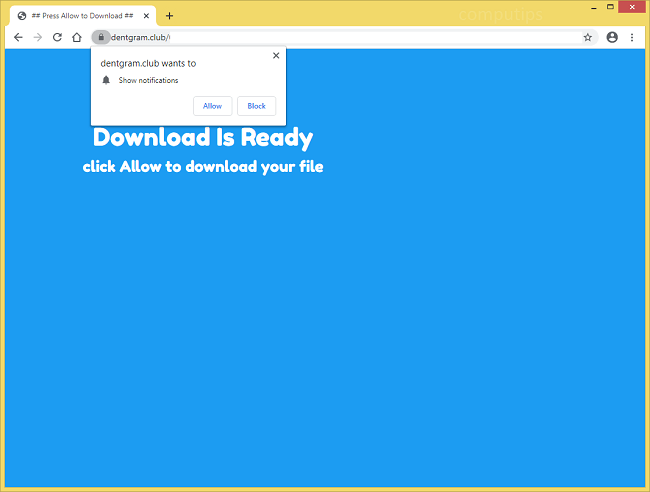
Dentgram.club is a dubious site that attempts to trick users into subscribing to its push notifications. The site may tell users that they have to click or tap Allow on its notifications confirmation pop-up box if they wish to access contents of some website, download a file, watch a video, and so on. Should a user click Allow, Dentgram.club notifications will begin popping up in a corner of his or her computer screen from time to time. Dentgram.club notifications will advertise various dubious websites, spam the user with scammy messages and clickbait links or offer him or her to download something. Dentgram.club site may start opening on your browser by itself if you have adware installed on your computer. This step-by-step guide will help you uninstall adware and remove Dentgram.club pop-ups and notifications from your PC.
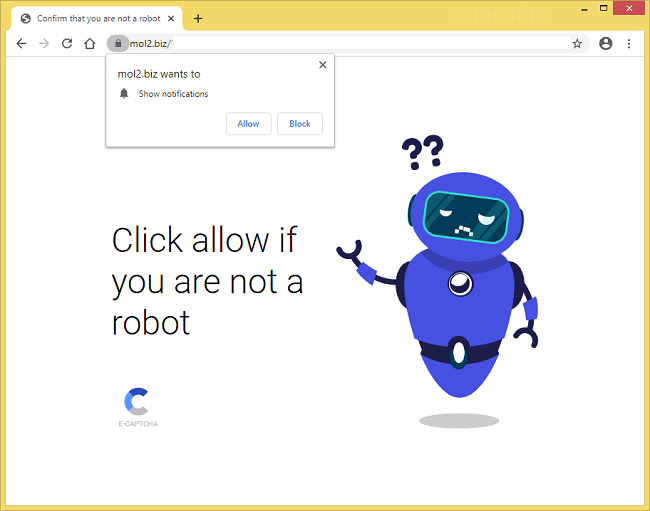
Mol2.biz is a shady website that tries to convince users that they have to turn on its notifications in order to watch a video, confirm that they are not robots, open a page, or something else along these lines. There are many websites that do the same, among them Mol3.biz, Mol5.biz, Mol6.biz, etc. If a user allows Mol2.biz notifications, those will start showing up on his or her screen periodically with clickbait links, ads, fraudulent messages or software offers. The notifications will appear in the lower-right corner of the screen on a Windows PC, in the top-right corner of the screen on a Macbook, and on the lockscreen on a smartphone. If Mol2.biz site keeps opening on your browser by itself, there may be adware installed on your device that is causing the pop-ups. This step-by-step guide will help you uninstall adware and remove Mol2.biz ads and notifications from your browser.
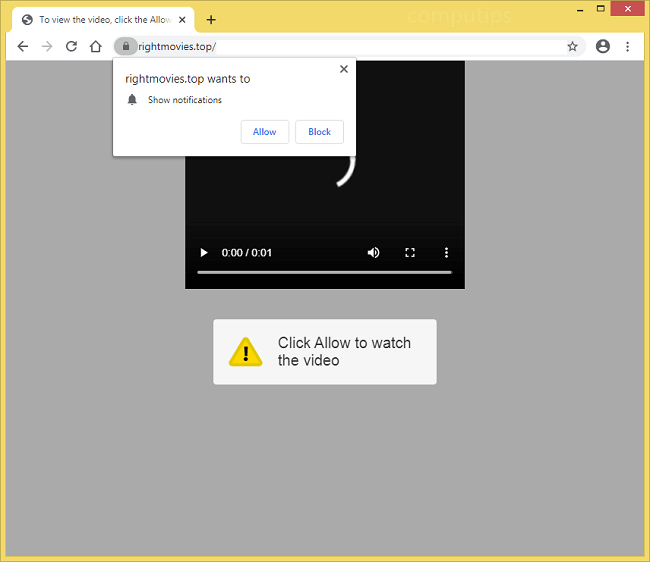
If Rightmovies.top site opens on your browser periodically, there might be adware installed on your computer. Rightmovies.top is one of many deceptive sites that attempt to trick users into enabling their browser notifications. Rightmovies.top may claim that users need to allow its notifications in order to play a video, start a download, confirm that they are of age, etc. If someone allows Rightmovies.top notifications, those will begin popping up periodically on the right side of the screen (or on the lockscreen on mobile devices). Rightmovies.top notifications will spam the user with ads for untrustworthy websites, scammy messages, clickbait links, and so on. You may follow this step-by-step guide to get rid of adware and remove Rightmovies.top notifications and pop-ups from your PC or phone.
If your browser started redirecting your searches to Search.skyenumerator.com (Sky Enumerator) all of a sudden, you probably have a browser hijacker installed on your Macbook. Browser hijackers alter default search engine, homepage and some other browser settings to make sure users visit time and again sites that browser hijackers promote. In addition to that, some browser hijacker keep track of users’ browsing activity (what websites they visit, what they search for on search engines) and use the data to display targeted ads to the users or sell it to other advertisers. Most of the time browser hijacker get installed on computers along with free programs or fake software updates that users download from the Internet. Some browser hijackers make extra effort so that users cannot remove them: hijackers create rogue user profiles or make themselves “installed by administrator”. You may follow this step-by-step guide to uninstall the browser hijacker and remove Search.skyenumerator.com (Sky Enumerator) from your browsers.

Systems that are infected with this ransomware run the risk of losing some files. This malware is designed to infect files globally. After scanning the system files will become unavailable. If file name has an extension in the name “.flowEncryption” (example: audio.flowEncryption) it means that this file is blocked.
Developers of FlowEncryption Ransomware use the locked files to their advantage. They offer victims to buy decryption tools

SportsHDSearchs browser is a virus that has the infection traits of a browser hijacker. After infiltrating the system it makes changes to the browser settings to promote the sportshdearchs.com search engine. It is able to infect absolutely any browser, be it Google Chrome, Mozilla Firefox or Internet Explorer. Changes in system settings will not only affect your system but also you. Due to the large amount of advertising you will not be able to work normally on the Internet. Ads will appear frequently and in every corner of the screen for you to accidentally click on. For deliberate clicking virus will collect personal information about you in order to know which sites you visit most often what you are interested in. When information is stolen, SportsHDSearchs browser will display ads with interesting topics for you to force you to click on them. More advertisements harm the system’s performance.
SportsHDSearchs browser will change your usual search engine. When you make a request you will be immediately redirected not to the desired site but to another malicious page.

EG83 ransomware is a malicious program from the Matrix ransomware family. Like all viruses of this type, EG83 ransomware blocks files on the computer and makes inaccessible for use. After the final infection a note from developers will appear on your screen