The MSDT exploit is a dangerous vulnerability in Microsoft Windows that allows hackers to perform “remote code execution”. In layman’s terms – this means that the MSDT exploit allows hackers to do anything they want with your computer. Maybe they’ll mine cryptocurrency, maybe they’ll steal your accounts, maybe they’ll install a ransomware program… anything is possible. It affects all modern Windows versions – Windows 7 and the newer versions are all vulnerable.
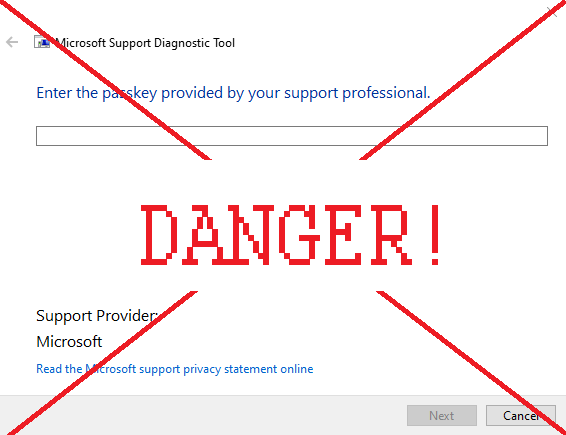
The exploit allows hackers to corrupt .docx and .rtf files (text documents), as well as Windows shortcuts, in such a way that it allows them to control your computer. This is done through a vulnerability in Microsoft Support Diagnostic Tool (MSDT), which is why it is called the MSDT exploit. In case of .docx files and shortcuts, the hacker needs the victim to open the file. However, .rtf files are even more dangerous – simply clicking on the file once, without opening it, is enough to be hacked.
Note that Microsoft Support Diagnostic Tool by itself is not dangerous. However, you should never see the window on the image above unless you’re interacting with Microsoft Support. If you saw this window randomly appear, or appear after you’ve opened a file – you’ve been infected.
This vulnerability is also known as Follina, and in the cybersecurity world, as CVE-2022-30190 and Mesdetty. So if you’ve heard one of these names – these are all just different names for this vulnerability.
Although this is a very serious flaw in Windows’s security, it can be easily fixed. This article will teach you how to fix MSDT exploit so you can be safe from the hackers trying to use this vulnerability.