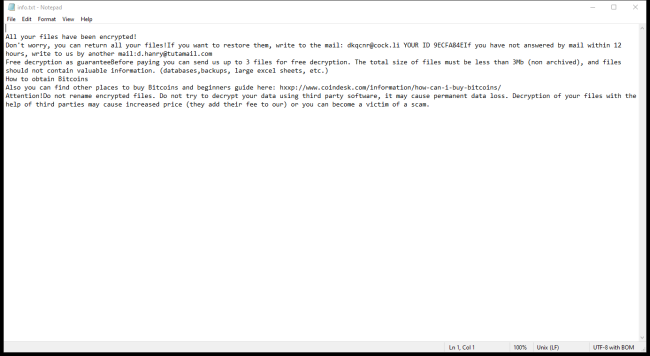
2000USD Ransomware is a malicious software that encrypts files on a victim's computer and demands a ransom of 2000USD in exchange for the decryption key. This type of ransomware typically infects computers through phishing emails, malicious websites, or software vulnerabilities. Once the ransomware is executed, it scans the victim's files and adds a specific file extension, such as .2000usd, to each encrypted file. This makes it impossible for the victim to access their files without the decryption key.
Category: Ransomware
Articles about ransomware – malware encrypting your personal files or stopping you from accessing your computer – and ways to remove it
How to remove Senanam Ransomware and decrypt .senanam files
Senanam Ransomware is a type of malicious software that encrypts files on a victim's computer, making them inaccessible until a ransom is paid. It typically infects computers through phishing emails, malicious websites, or software vulnerabilities. Once installed, Senanam Ransomware adds a specific file extension to encrypted files, such as .senanam, making it clear which files have been affected. The ransomware uses advanced encryption algorithms to lock the files, making it nearly impossible to decrypt them without the decryption key.
How to remove Anonymous Arabs Ransomware and decrypt .encrypt files
Anonymous Arabs Ransomware is a dangerous type of malware that infects computers and.encrypts files, making them inaccessible to users. It typically spreads through malicious email attachments, infected websites, or software downloads. Once a computer is infected, the ransomware adds specific file extensions such as .encrypt to all encrypted files, making them impossible to open or use. The ransomware uses advanced encryption algorithms to lock files, making it extremely difficult to decrypt them without the decryption key.
How to remove XFUN Ransomware and decrypt .xfun files
XFUN ransomware is a malicious software that infects computers by encrypting files and demanding a ransom for their decryption. It often spreads through malicious email attachments, software downloads, or compromised websites. Once it infects a computer, XFUn ransomware adds the .xfun extension to encrypted files, making them inaccessible to the user.
How to remove Rapax Ransomware and decrypt .rapax files
Rapax Ransomware is a type of malicious software that encrypts files on a victim's computer and demands a ransom in exchange for the decryption key. It typically infects computers through phishing emails, malicious websites, or software vulnerabilities. Once a computer is infected, Rapax Ransomware adds a specific file extension to all encrypted files, such as .rapax, making them inaccessible to the user.
How to remove Cebrc Ransomware and decrypt .cebrc files
Cebrc Ransomware is a malicious software program designed to encrypt files on a victim's computer and demand a ransom in exchange for the decryption key. It typically infects computers through phishing emails, malicious websites, or software vulnerabilities. Once the ransomware gains access to a system, it encrypts files using a strong encryption algorithm, making them inaccessible to the user.
How to remove Jinwooks Ransomware and decrypt .jinwooksjinwooks files
Jinwooks ransomware is a type of malicious software that infects computers by encrypting files and demanding a ransom for their release. Once a computer is infected with Jinwooks ransomware, it will add a specific file extension to all encrypted files, typically .jinwooks. This makes it easy for victims to identify which files have been affected by the ransomware.
How to remove Geometrical Ransomware and decrypt .geometrical files
Geometrical Ransomware is a type of malicious software that infects computers by encrypting files and demanding a ransom for their decryption. It typically spreads through phishing emails, malicious websites, or exploit kits. Once a computer is infected, Geometrical Ransomware adds a specific file extension to the encrypted files, such as .geometrical, making them inaccessible to the user.
How to remove Dkq Ransomware and decrypt .dkq files
Dkq Ransomware is a malicious software that infects computers by encrypting files and demanding a ransom for their decryption. This ransomware typically spreads through phishing emails, malicious attachments, or compromised websites. Once a computer is infected, Dkq Ransomware adds a specific file extension to the encrypted files, making them inaccessible to the user.
How to remove El Dorado Ransomware and decrypt .00000001 files
El Dorado Ransomware is a dangerous malware that infects computers through malicious email attachments, fake software updates, or by exploiting vulnerabilities in the system. Once installed, it encrypts the files on the infected computer, adding the extension ".eldorado" to the encrypted files. The ransomware uses a strong encryption algorithm to lock the files, making it nearly impossible to decrypt them without the decryption key.