What is YGKZ ransomware
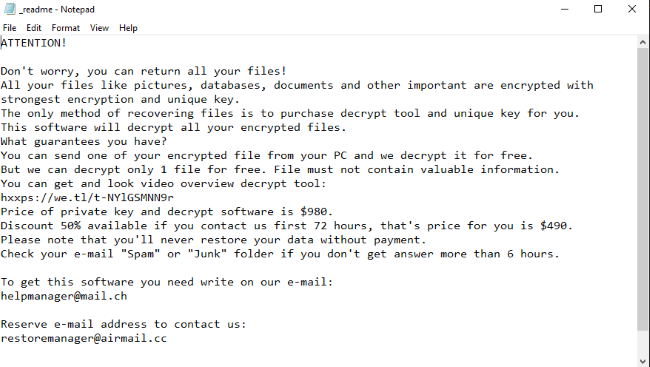
YGKZ is a new ransomware virus, that belongs to STOP/DJVU file-encryption-ransomware family. In the most cases, YGKZ ransomware spreads by the means of malicious executables and installers. Such files are usually promoted as free/cracked software and distributed through free-file sharing services and torrent trackers. However, criminals can easily infect computers remotely the means of remote access ports and terminals. When YGKZ gets into the operating system, it begins to modify registry folder and infects system processes. Then YGKZ virus begins the encryption process. As the result, your files get new “.YGKZ” extensions. At the same time YGKZ drops the ransom note called “_readme.txt”. By the means of such note criminals try to assure you, that the only way out is to pay them. We strongly recommend you to avoid any contact with them, because there is no any guarantee, that they will decrypt the files. Moreover, it’s easy for them to make the situation much worse. So, if you need to remove YGKZ ransomware and decrypt “.YGKZ” files, you’d better use our guide!
Article’s Guide
- How to remove YGKZ ransomware from your computer
- How to Recover Files Encrypted by YGKZ Ransomware
- How to decrypt .YGKZ files
- Manually decrypt .YGKZ files
How to Remove YGKZ Ransomware
If you have working backups of your encrypted files or you are not going to try and recover lost files, then scan your computer with one or several antivirus and anti-malware programs or reinstall the operating system altogether.
How to Recover Files Encrypted by YGKZ Ransomware
If you want to recover files encrypted by ransomware you can either try to decrypt them or use methods of file recovery.
Ways to decrypt the files:
- Contact the ransomware authors, pay the ransom and possibly get the decryptor from them. This is not reliable: they might not send you the decryptor at all, or it might be poorly done and fail to decrypt your files. Moreover, criminals often deceive the victims and make them pay twice or even send another virus instead of the decryption tool.
- Wait for security researchers to find some vulnerability in the ransomware that would allow you to decrypt files without paying. This turn of events is possible but not very probable: out of thousands of known ransomware variants only dozens were found to be decryptable for free. Here you can find the list of trustworthy decryption services.
- Use recovery tool to recover your data.
- Try to decrypt “.YGKZ” files manually.
Decrypt “.YGKZ” files with decryption services
Every day malware hunters inspect new examples of ransomware viruses and find their vulnerabilities in order to get the decryption keys or create their own decryptor. So if you are lucky enough, probably the one of the services already has a solution on how to decrypt “.YGKZ” files. If you are unlucky, try the next method.
Decrypt .YGKZ files with Emsisoft decryptor
Emsisoft decryptor use the one of the biggest databases and contain information about hundreds of ransomware families.
Decrypt .YGKZ files with NoMoreRansom decryptor
NoMoreRansom is a new decryption service, which gives an opportunity to decrypt a wide range of extensions. So, Try it and don’t worry, your files will be safe.
Decrypt .YGKZ files with Kaspersky decryptors
Nowadays Kaspresky is one of the world’s leading suppliers of antivirus programs. Recently, they decided to provide decryption service. However, their decryption service is rather new it still might help you to recover your data. Click here and you will be redirected to the decryption page.
Decrypt .YGKZ files with Dr. Web decryptors
Dr. Web is one of the oldest companies, which provide antivirus protection. Their decryption system is rather new, but it can help you. Click here and you will be redirected to the decryption page.
If these decryptors didn’t help you, you can always try to recover your data from the shadow copies of files. So try the next method.
Use File Recovery Tools to Recover Files
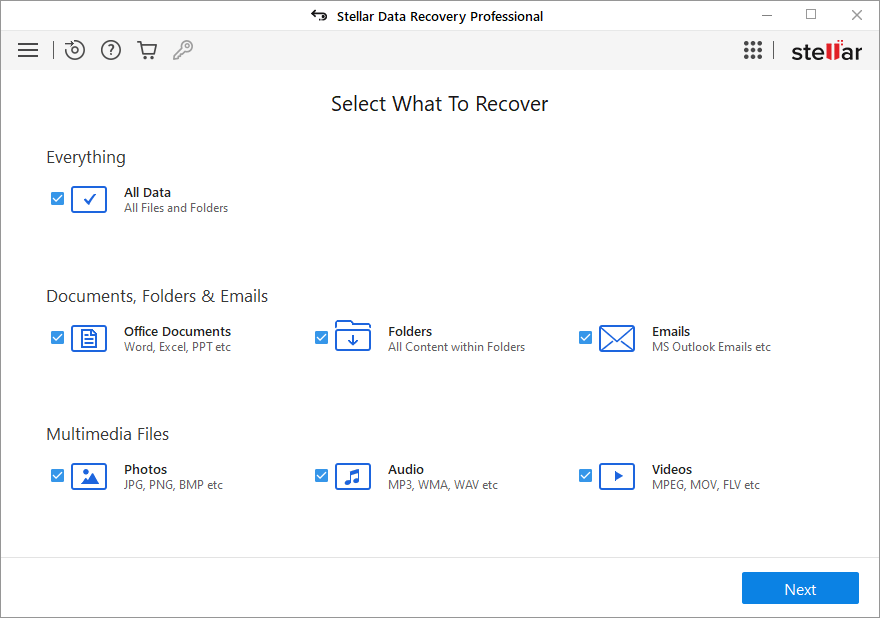
If the above mentioned decryption services didn’t help you, you may try to recover your data with the help of recovery tools. We strongly advice you to use Stellar Data Recovery, as far as it has proven it’s abilities to recover the data.
Screenshot:
About Stellar Data Recovery
Now that you have your recovered or still encrypted files on an external device, it is time to scan your computer with AV and anti-malware software or, better yet, reinstall the operating system, to fully get rid of possible ransomware traces. Remember to also scan your external device before putting files back on your computer!