Error in your IMAP/POP3 mail server can be a frustrating issue for users who rely on these protocols to access their emails. These errors can occur for a variety of reasons, such as incorrect server settings, network issues, or server maintenance. When an error occurs, users may experience difficulties in sending or receiving emails, accessing their mailboxes, or syncing their devices with the mail server.
How to remove Hyperliquid ($HYPE) Airdrop pop-ups
Hyperliquid ($HYPE) Airdrop is a distribution of free tokens to users of the Hyperliquid platform. The airdrop is a marketing strategy used by the project to increase awareness and adoption of their cryptocurrency. Users can receive free $HYPE tokens simply by participating in the airdrop program, which usually involves completing certain tasks or holding a specific amount of tokens in their wallet.
How to remove Qeza Ransomware and decrypt .qeza files
Qeza Ransomware is a malicious software that infects computers through various means, such as phishing emails, malicious websites, or software vulnerabilities. Once it infiltrates a system, Qeza encrypts files on the infected machine, adding a ".qeza" extension to each encrypted file. The ransomware uses a strong encryption algorithm to lock the files, making them inaccessible to the user.
How to remove Klaytn ($KLAY) Airdrop pop-ups
Klaytn ($KLAY) Airdrop is a promotional event conducted by the Klaytn blockchain platform to distribute free tokens to its users. The airdrop is typically used as a marketing strategy to increase awareness of the project and reward early supporters. Participants can receive a certain amount of KLAY tokens for completing specific tasks or meeting certain criteria set by the Klaytn team.
How to remove Mailbox Update pop-ups
Mailbox Update is a pop-up message that appears in web browsers, typically when users are browsing the internet. This message usually informs users that their mailbox needs to be updated, prompting them to click on a link to take action. However, Mailbox Update is often associated with malicious activities such as phishing scams and malware installations.
How to stop Your System Has Been Cracked email scam
Your System Has Been Cracked email spam is a common type of phishing scam where cybercriminals send fraudulent emails claiming that the recipient's system has been compromised. These emails often contain alarming messages, such as threats to release private information or install malware if a ransom is not paid. The goal of these scams is to scare recipients into taking immediate action without thinking critically, leading them to click on malicious links or provide personal information.
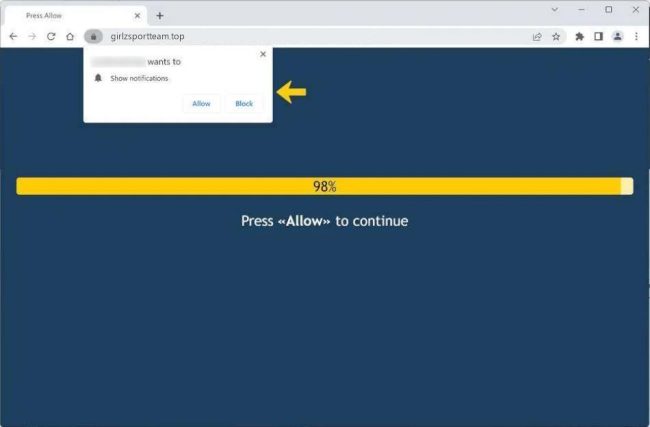
How to remove Girlzsportteam.top
Girlzsportteam.top is a malicious website that infects computers through various deceptive tactics. It typically spreads through misleading online advertisements, software bundling, or malicious email attachments. Once a user visits the website, they may be prompted to allow notifications, which can then lead to a barrage of unwanted pop-up ads and notifications.
How to remove the fake deBridge website pop-ups
The fake deBridge website is a fraudulent website that mimics the legitimate deBridge website in order to deceive users into providing personal information or downloading malicious software. These fake websites often look very similar to the real website, making it difficult for users to differentiate between the two.
How to stop Wells Fargo – Account Verification Required email scam
Wells Fargo - Account Verification Required email spam is a phishing scam that targets individuals by posing as a legitimate communication from Wells Fargo, a major financial institution. The email typically informs recipients that their account needs verification or updating, and prompts them to click on a link to provide their personal and financial information. This type of phishing campaign is designed to steal sensitive data such as login credentials, credit card numbers, and other personal information.
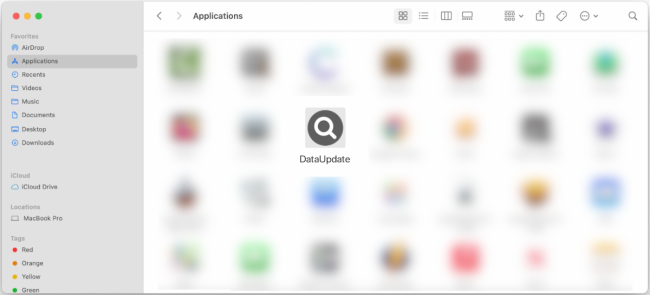
How to remove DataUpdate (Mac)
DataUpdate is a type of malware that infects Mac computers, typically through deceptive methods such as fake software updates or malicious email attachments. Once installed on a Mac system, DataUpdate can access and steal sensitive information, track user activity, and even take control of the computer remotely. This malware can also disrupt the normal functioning of the system, slowing it down and causing crashes.