What is “Your System Has Been Cracked” Email Spam
Subject: Re:
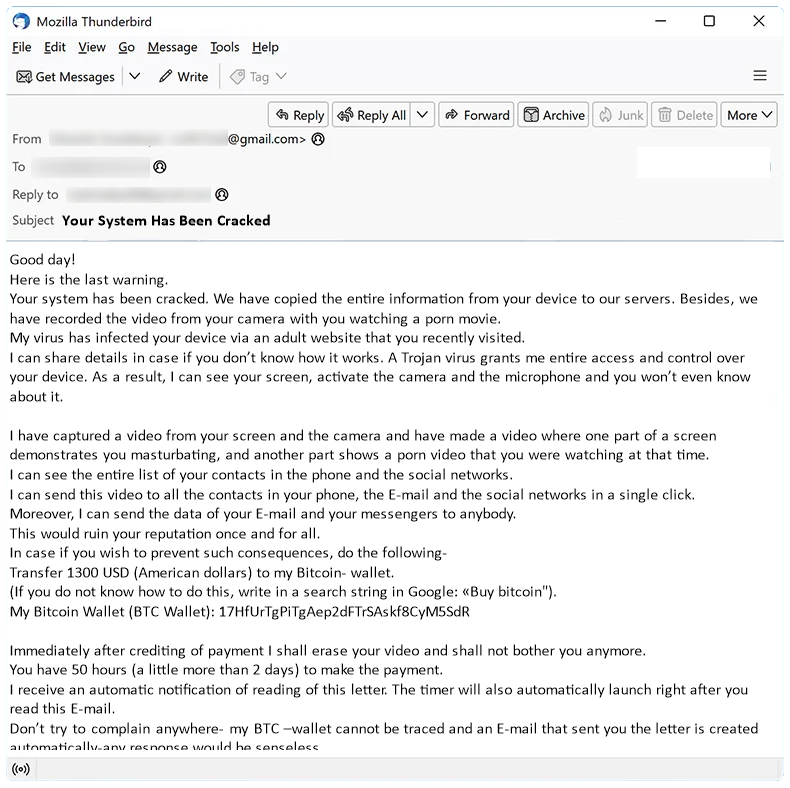
Good day!
Here is the last warning.
Your system has been cracked. We have copied the entire information from your device to our servers. Besides, we have recorded the video from your camera with you watching a porn movie.
My virus has infected your device via an adult website that you recently visited.
I can share details in case if you don’t know how it works. A Trojan virus grants me entire access and control over your device. As a result, I can see your screen, activate the camera and the microphone and you won’t even know about it.
I have captured a video from your screen and the camera and have made a video where one part of a screen demonstrates you masturbating, and another part shows a porn video that you were watching at that time.
I can see the entire list of your contacts in the phone and the social networks.
I can send this video to all the contacts in your phone, the E-mail and the social networks in a single click. Moreover, I can send the data of your E-mail and your messengers to anybody.
This would ruin your reputation once and for all.
In case if you wish to prevent such consequences, do the following-
Transfer 1300 USD (American dollars) to my Bitcoin- wallet.
(If you do not know how to do this, write in a search string in Google: «Buy bitcoin").
My Bitcoin Wallet (BTC Wallet): 17HfUrTgPiTgAep2dFTrSAskf8CyM5SdR
Immediately after crediting of payment I shall erase your video and shall not bother you anymore.
You have 50 hours (a little more than 2 days) to make the payment.
I receive an automatic notification of reading of this letter. The timer will also automatically launch right after you read this E-mail.
Don’t try to complain anywhere- my BTC –wallet cannot be traced and an E-mail that sent you the letter is created automatically-any response would be senseless.
Should you try to share this E-mail with somebody, the system will automatically send a request to the servers and they will start sending the entire information to social networks.
The change of passwords of social networks, an E-mail and the device would be senseless either as the whole data has already been downloaded to cluster of my servers.
I wish you luck and don’t do something stupid. Consider your reputation.
Your System Has Been Cracked email spam is a common type of phishing scam where cybercriminals send fraudulent emails claiming that the recipient’s system has been compromised. These emails often contain alarming messages, such as threats to release private information or install malware if a ransom is not paid. The goal of these scams is to scare recipients into taking immediate action without thinking critically, leading them to click on malicious links or provide personal information.
Your System Has Been Cracked spam campaigns typically infect computers through phishing emails that contain malicious attachments or links. Once a user interacts with the email, they may inadvertently download malware onto their system, allowing cybercriminals to gain access to sensitive data or control over the infected device. The risks of interacting with Your System Has Been Cracked email scams include financial loss, identity theft, and compromised personal information. It is important for individuals to be cautious when receiving unsolicited emails and to verify the authenticity of the sender before taking any action.
How to stop email spam like “Your System Has Been Cracked”
You can use an anti-spam filter which will block most known sources of spam before they even reach your inbox. MailWasher is a program you may try. It filters spam and lets you preview emails on a server without downloading them onto your computer. MailWasher has customizable spam filters, uses bayesian filtering and works with all major email programs: Outlook, Outlook Express, Thunderbird, GMail, etc.
Types of spam email
Spam email messages can be approximately divided into three categories: those that prompt you to download and run something, those that ask for your personal data, and those asking you to make payments. Let’s take a closer look at each one so we can better protect ourselves from these scams.
-
Emails with attachments
In the first case the email contains an attachment which it prompts you to open. Those attachments may consist of executable files or they may be Microsoft Word or Excel documents containing malicious macro scripts. Once you launch the executable file or allow the document to run its macros, malware downloads onto your device and wreaks all kinds of havoc with it.
The malware may range from adware showing extra ads on your browsers to ransomware that encrypts your files and aks for payment to decrypt them.
-
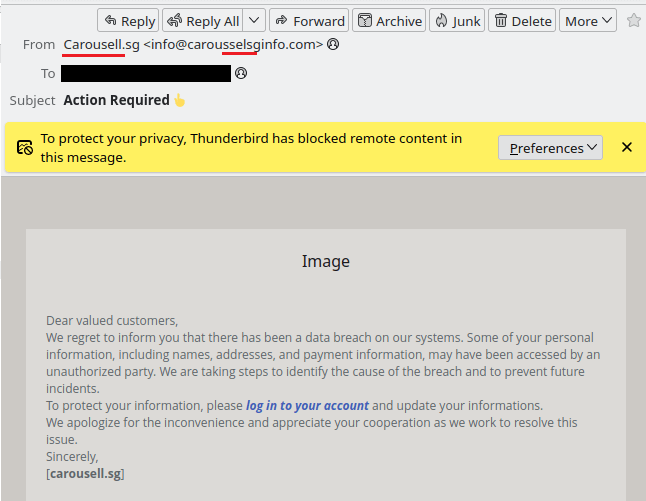
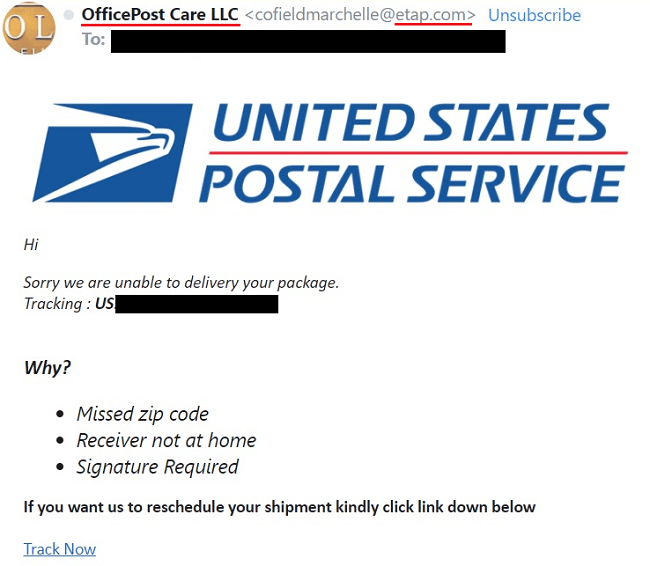
Phishing emails
The second type of spam (phishing emails) try to trick you into entering your name, logins, passwords, credit card details, etc. on what you think are legitimate and respectable websites.
Those emails usually pretend to be messages from well-known websites that you are probably registered on, and prompt you to follow a link to their site for some reason (for example, there is something wrong with your account). The provided link leads to fake site of course, and the data you enter ends up in the hands of cybercriminals.
-
Advance-fee scam and sextortion scam emails
Finally there are the emails urging people make payments. These can be further divided into two types: the first type, asking people to invest into something, to pay some money now and get back much more later (the advance-fee scam); the second one, scaring people into paying to prevent something bad from happening.
An example of the first one is the well-known Nigerian Prince email. A example of the second is sextortion scam: emails that claim that the email author has access to the victims’s web cam and has the victims intimate videos, which the criminal threatens to publish unless paid off.
How to find out that the email is scam
- Check the sender’s address – if the address doesn’t match up with what you expect from that company, then it’s very likely that the email is scam. Be aware though that the sender address can be faked, so if the address looks legitimate it is not guaranteed that the email is legit.
- Look for spelling and grammar mistakes and weird phrasing – real emails from reputable companies are far less likely to have those.
- Watch for urgent requests – legitimate companies will never ask customers for sensitive information such as credit card numbers via email, so if an email suddenly asks for urgent action like requesting payment details within few hours, chances are high this could potentially be a scam attempt.
How to protect yourself from email scam
- Use an email filtering service – email filtering services like MailWasher Pro allow you to filter out unwanted messages before they reach your inbox. These services use sophisticated algorithms to identify suspicious content in incoming emails and block them automatically so that only legitimate messages make it through the filter.
- Avoid clicking on suspicious links – if you receive an email with a link that looks suspicious, do not click on it! Even if the sender appears familiar, chances are high that the link is malicious and could lead you down a path of malware infection or identity theft. It is best not to open any unknown links at all.
- Don’t respond directly – never reply directly to spam emails as this will confirm for spammers that your address is active which may result in more unsolicited mail being sent your way. Instead, mark these messages as “Spam” within your email client/service provider so that their filters can better detect similar types of mail next time.
- Keep software up-to-date – make sure all software installed onto devices such as computers and smartphones is kept up-to date with latest security patches released by developers; this helps reduce risk posed by cyber criminals who exploit vulnerabilities found in outdated versions of programs including email clients.
- Use anti virus protection – install reputable antivirus solutions onto any device receiving emails; most modern day anti viruses come equipped with advanced features such as real time scanning which help detect potential threats immediately upon opening files attached to emails.
