What Is Cyclostomatous?
Cyclostomatous is a type of malware that specifically targets Mac computers. It is a sophisticated form of malware that is designed to infect Mac operating systems and carry out malicious activities without the user’s knowledge. Cyclostomatous malware can infiltrate a Mac system through various means, such as phishing emails, malicious websites, or software downloads.
Once Cyclostomatous infects a Mac computer, it can perform a range of harmful actions, such as stealing sensitive information, logging keystrokes, and taking screenshots of the user’s activity. It can also install additional malware or backdoors, allowing cybercriminals to gain remote access to the infected system. Cyclostomatous is known for its ability to evade detection by traditional antivirus software, making it challenging to detect and remove from an infected Mac. To protect against Cyclostomatous and other malware threats, Mac users should practice safe browsing habits, keep their operating system and software up to date, and use reputable antivirus software.
How to Remove Cyclostomatous:
- Remove Cyclostomatous Automatically
- Delete Rogue Applications
- Remove Rogue Profiles from Macbook
- Remove Cyclostomatous From Browsers
- How to Protect Your PC From Cyclostomatous and Other Adware
Remove Gloss Glamour Automatically
You may try to remove the adware automatically or use the manual instructions provided below.
However it is still recommended that you scan your system with a good antivirus or anti-malware tool, to find and remove other possible malware and PUPs (potentially unwanted programs) that may have been installed along with Cyclostomatous.
Some alternatives:
Spyhunter (macOS and Windows)
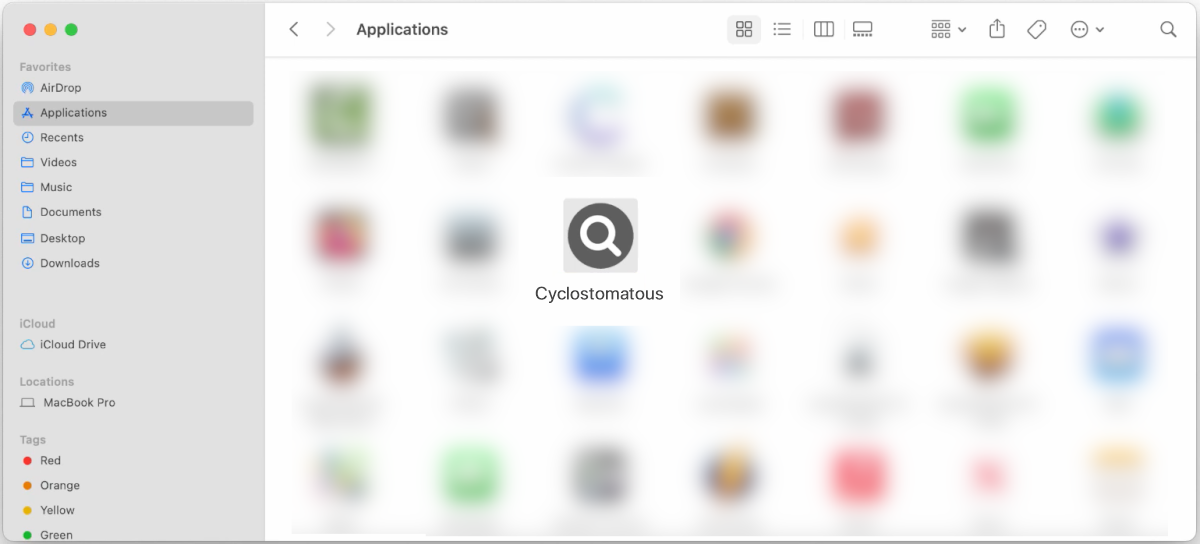
Delete Rogue Applications:
Go to Applications folder and delete new and suspicious apps.
- On the top menu select Go => Applications.
- Drag an unwanted application to the Trash bin.
- Right-click on the Trash and select Empty Trash.
Remove Rogue Profiles from Macbook:
- Open System Preferences.
- Click on Profiles.
- Click the minus button below to delete rogue settings.
Remove Cyclostomatous from browsers:
Remove Cyclostomatous and other new and unfamiliar extensions.
Remove Cyclostomatous from Safari:
- On the top menu select Safari => Preferences (or Settings).
- Select Extensions tab.
- Select an extension you want to delete and click Uninstall button under the extension’s description.
Remove Cyclostomatous from Google Chrome:
- Click on three dots menu button
 .
. - Select More tools => Extensions.
- Find an extension you want to delete and click REMOVE under it.
- Click Remove in the dialog box.
Cyclostomatous Removal from Mozilla Firefox:
- Click on menu button
 and select Add-ons.
and select Add-ons. - Go to the Extensions tab.
- To uninstall an add-on, click on three dots button next to it and select Remove.
How to Protect Your Mac From Cyclostomatous and Other Adware:
- Use an antivirus:Get a powerful anti-malware software, capable of detecting and eliminating PUPs. Having several on-demand scanners would be a good idea too.
- Keep macOS and apps updated: Regularly update your macOS and applications to patch security vulnerabilities and strengthen your system against malware.
- Use ad-blockers:Download and use Adguard, uBlock Origin or one of the other trustworthy extensions for blocking third-party advertisements on websites.
- Download from trusted sources: Only download apps, software, and files from trusted sources like the Apple App Store to minimize the risk of malware infections.
- Read dialogue boxes carefully: Pay close attention to dialogue boxes to avoid inadvertently installing malware.
- Be cautious with email attachments and links: Avoid opening suspicious email attachments and clicking on unfamiliar links to prevent malware infiltration.
 .
.