How to Get Windows 8.1 on a Macbook
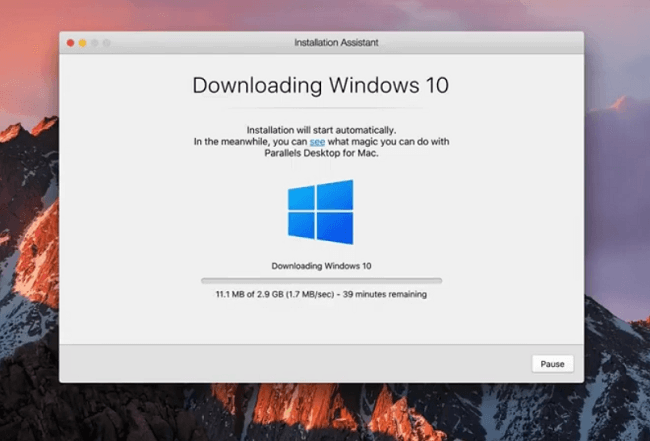
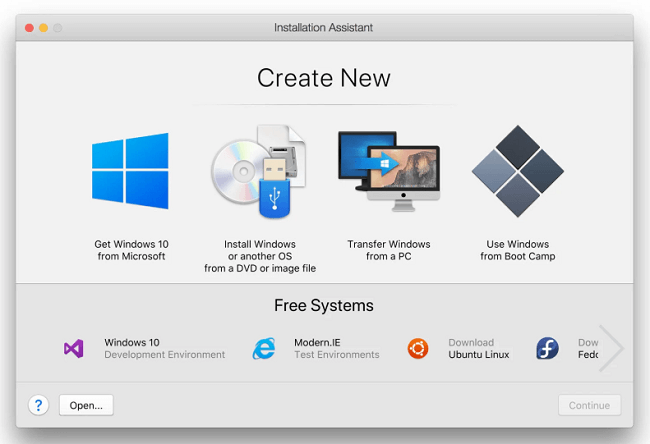
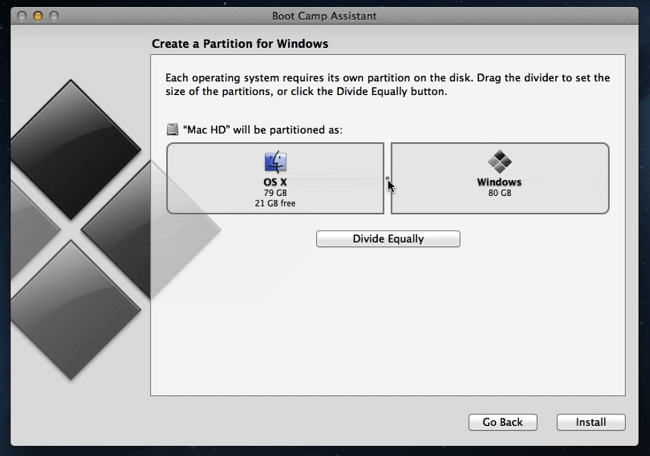
If you need to run Windows 8.1 on a Macbook, there are a few ways to do it: you can use Mac’s BootCamp Assistant or download and use a virtual machine like Parallels Desktop, VMware Fusion or VirtualBox. Unfortunately, installing Windows 8 via BootCamp will probably not work if your Macbook is newer than 2016. In that case virtualization software should still work if you have a Windows 8.1 license key. In this article we describe pros and cons of each method so that you can decide for yourself which one to use.