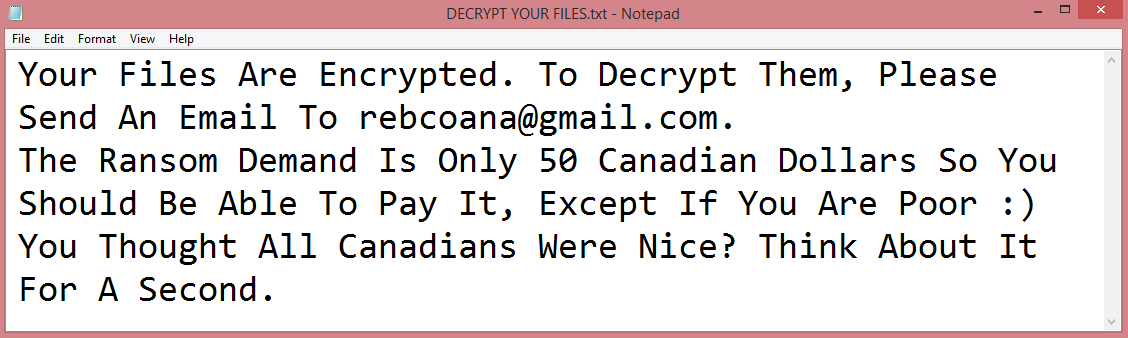
![Vohuk ransom note:
[~] Vohuk Ransomware V1.3
>>> What's happened?
ALL YOUR FILES ARE STOLEN AND ENCRYPTED.
To recovery your data and not to allow data leakage, it is possible only through purchase of a private key from us.
>>> What guarantees?
We are not a politically motivated group and we do not need anything other than your money.
Before paying you can send us up to 2 files for free decryption.
The total size of files must be less than 2MB(non archived).
files should not contain valuable information. (databases, backups, large excel sheets, etc.)
>>> CONTACT US:
Please write an email to both: payordiebaby@tutanota.com & payordiebaby69@msgsafe.io
Write this Unique-ID in the title of your message: [REDACTED]
>>> ATTENTION!
Do not delete or rename or modify encrypted files.
Do not try to decrypt using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price(they add their fee to our).
We use strong encryption, nobody can restore your files except us.
The price depends on how fast you contact with us.
remember to hurry up, as your email address may not be available for very long.
All your stolen data will be loaded into cybercriminal forums/blogs if you do not pay ransom.
If you do not pay the ransom we will attack your company repeatedly again.
This is the end of the note. Below you will find a guide explaining how to remove Vohuk ransomware.](https://www.computips.org/wp-content/uploads/2022/11/how-to-remove-vohuk-ransomware.png)
What is Vohuk ransomware?
Vohuk is a malware program more specifically categorized as ransomware. It utilizes cryptographic algorithms to encrypt all user files on the infected computer. These encrypted files cannot be accessed; to view or edit them, decryption is necessary. This is how this virus works, it offers to decrypt the files it encrypted. The hackers demand money for this procedure, of course.
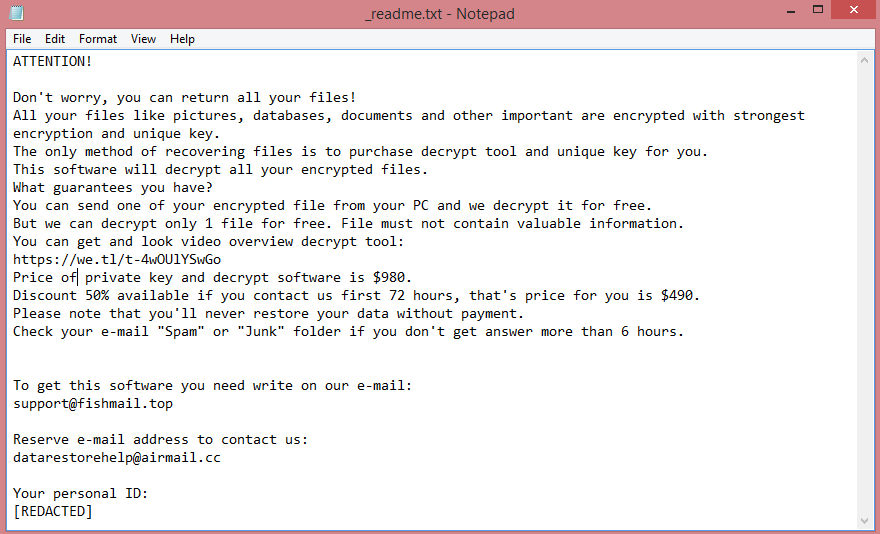
Vohuk, just like every other ransomware program, leaves a ransom note. In this case, it is called “README.txt”. The full text of the note is available on the image above. That said, it doesn’t contain much information at all. The hackers don’t mention the price, only their e-mail addresses.
The virus also renames files while encrypting them. The name of each file is replaced with a string of random characters, while the extension is replaced with .Vohuk file extension.
While contacting the criminals and paying the ransom is an option, it is generally not a good one. Often, they will not decrypt your files even after payment. Instead they will disappear or try to get more money from you. The guide below will explain how to remove Vohuk ransomware and decrypt .Vohuk files without having to deal with the hackers.
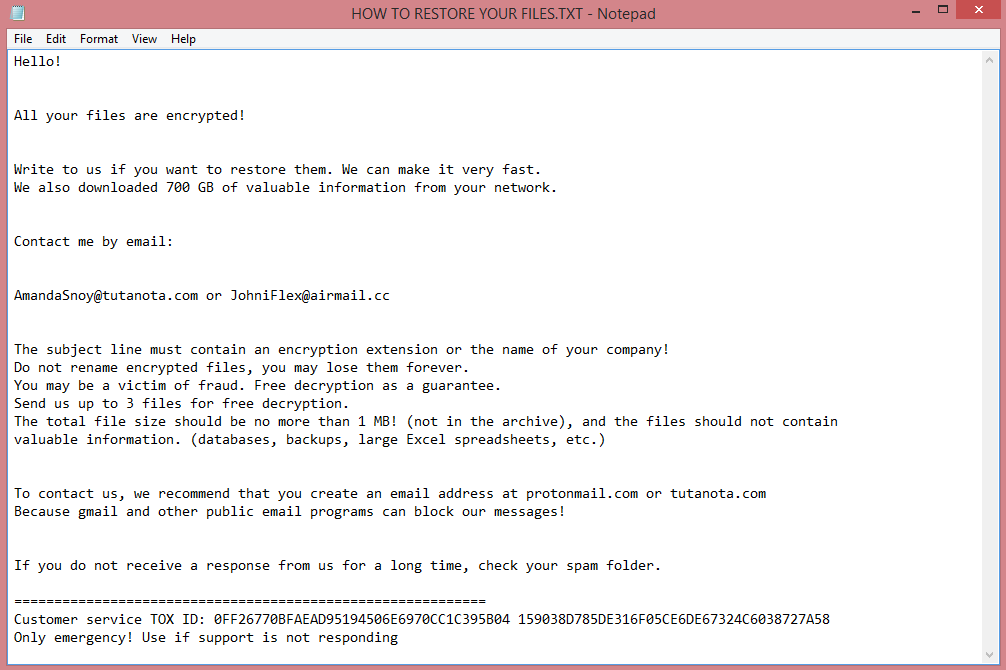
![CryptBIT 2.0 ransom note:
Hello!
Now your files are crypted with the strongest millitary algorithms RSA4096 and AES-256.
In addition, all encrypted files have been sent to our server
and in the event of non-payment within 7 days,they will be made public.
Warning!
Do not rename encrypted files.
Do not try to decrypt your data using third party software.
You can only do damage to your files, lose your money and time.
In order to confirm that we are not scammers, you can send 2-3 files to the email address below.
Files should be less than 5 MB and contain no valuable data (Databases, backups, large excel sheets, etc.).
Please don't forget to write the name of your company in the subject of your e-mail.
You will receive decrypted samples.
To recover all files you must contact us for a private quote by the contact email.
You have to pay for decryption in Bitcoins.
P.S. Remember, we are not scammers.
We don't need your data or information but after 7 days all files and keys will be deleted automatically.
Write to us immediately after infection
All your files will be restored. We guarantee.
Contact email:
cryptbit2.0@protonmail.com
BTC wallet:
[REDACTED]
Have a nice day
CryptBIT 2.0 ransomware group
This is the end of the note. Below is a guide explaining how to remove CryptBIT 2.0 ransomware.](https://www.computips.org/wp-content/uploads/2022/11/how-to-remove-cryptbit-2.0-ransomware.png)
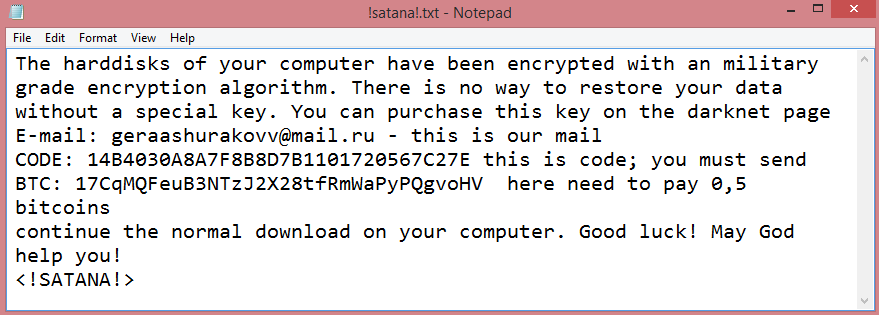
![Anthraxbulletproof ransom note:
Your computer was infected with a ransomware virus. Your files have been encrypted and you won't
be able to decrypt them without our help.What can I do to get my files back?You can buy our special
decryption software, this software will allow you to recover all of your data and remove the
ransomware from your computer.
How do I pay, where do I get Bitcoin?
Purchasing Bitcoin varies from country to country, you are best advised to do a quick google search
yourself to find out how to buy Bitcoin.
Payment informationAmount: 10 000 American Dolar ( Convert it in Bitcoin )
Bitcoin Address: [REDACTED]
After Sending Bitcoin Send us a message on telegram : @anthraxlinkers
This is the end of the note. Below you will find a guide explaining how to remove Anthraxbulletproof ransomware.](https://www.computips.org/wp-content/uploads/2022/11/how-to-remove-anthraxbulletproof-ransomware.png)